User Controls
Arbitrary code execution.
-
2022-09-21 at 2:47 PM UTCSorry for the vague title but if i make it overly technical people's eyes will just glaze over and click on another thread instead. Anyway i currently can't access any of my Windows VMs because my server was having some technical difficulties, which are being worked on.
Anyway i was wondering whether PrintUI.exe still loads an arbitrary PrintUI.dll from %ProgramData% or it's immediate path instead of the system directory on wanblows. Obviously at the enterprise level this will be well taken care of but your average user doesn't know how incompetent Micrococks is.
If it has been fixed in recent updates that's fine but a year ago this was still a great vector not only for arbitrary code execution but privilege escalation as well. Micro$oft has been aware of this since 2014.
To test run:
COPY "%SystemRoot%\System32\ShUnimpl.dll" "%ProgramData%\PrintUI.dll"
RENAME "%ProgramData%\WRITABLE.LOG" PrintUI.exe
START "" /WAIT "%ProgramData%\PrintUI.exe"
CERTUTIL.exe /ERROR %ERRORLEVEL%
If the new PrintUI works as intended you have a problem. ShUnimpl.dll is supposed to get rid of obsolete shell functions, by letting them error out properly and prevent any shenanigans. PrintUI.exe does not comply with this though, and if/when it doesn't write a stager, shell, or cryptotrojan or anything you can think of really. Compile it for windows as DLL, and get it to "C:\Windows\System32\Tasks_Migrated\PrintUI.dll".
Now on the target box copy PrintUI.exe from %ProgramData% to the directory specified above and run it. It's going to load your malicious DLL, auto elevate it to admin and run your code. That's a game over for the box in question. -
2022-09-30 at 12:16 PM UTCNo answers huh, i guess all i can conclude is that i am a level 97 Cyber Security wizard and no one is even close to my level and therefore has nothing to contribute. Which is kind of unfortunate.The following users say it would be alright if the author of this post didn't die in a fire!
-
2022-10-23 at 9:46 PM UTCSorry. Im more of a web application type. Also I dont use Windows.
But this stuff on Linux would be cool. -
2022-10-23 at 10:07 PM UTCi use windows quite a lot. even for programming. i use windows so much i use a window manager. i think it's called enlightenment, it's really good.The following users say it would be alright if the author of this post didn't die in a fire!
-
2022-10-23 at 10:09 PM UTC
-
2022-10-23 at 10:11 PM UTC
-
2022-10-24 at 12:22 PM UTC
Originally posted by troon don't be sad, i just like to shit on sophie's threads because he talks so much shit. it's fun!
i talk the best shit, many experts they tell me: Soph, the shit you talk is excellent. It's true. Believe me. But you didn't provide any insight into the subject matter i was posting about.
Real talk, may i ask what your background is in Computer Science? -
2022-10-24 at 1:44 PM UTC
-
2022-10-24 at 1:49 PM UTC
-
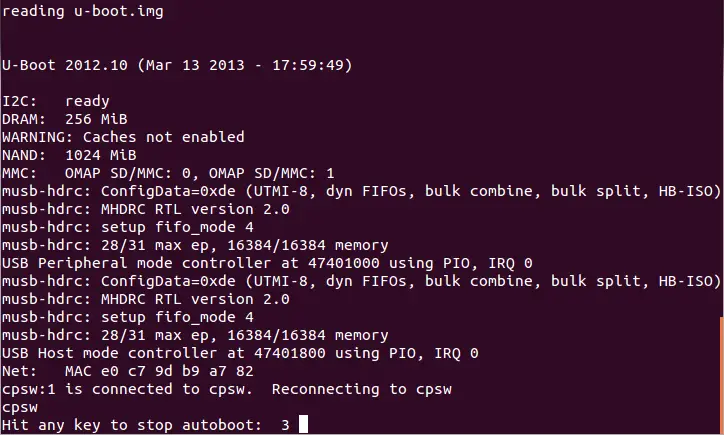
2022-10-24 at 1:55 PM UTCHit any key.
-
2022-10-24 at 1:58 PM UTC
-
2022-10-24 at 2:15 PM UTC
-
2022-10-24 at 11:09 PM UTCWell shit.
-
2022-10-25 at 3:28 AM UTC
-
2022-10-25 at 4:42 AM UTCThe best way is take a old RAT that's detected and make it fully undetectable by changing just enough code to evade the strings in the viral definitions. You can use 10 or 15 of the best virus scanners out there to check your results after each code adjustment. Eventually, you get a really good RAT that's FUD. Then you bind it to some program and upload it everywhere and bind an ICQ notification to it to call out to the FTP server log to pick up the IPs later. Can't get any easier than that.
-
2022-10-25 at 9:02 AM UTC
Originally posted by Sophie When troon says i talk a lot of shit. he's not saying i talk out of my ass, he just thinks i'm obnoxious.
i'm pretty sure you misunderstood migh's "well shit", it didn't seem to be intended as you read it. but i do note how your interpretation of my words influences your thinking. -
2022-10-25 at 4:47 PM UTC
Originally posted by ⠀⠀⠀⠀⠀⠀ The best way is take a old RAT that's detected and make it fully undetectable by changing just enough code to evade the strings in the viral definitions. You can use 10 or 15 of the best virus scanners out there to check your results after each code adjustment. Eventually, you get a really good RAT that's FUD. Then you bind it to some program and upload it everywhere and bind an ICQ notification to it to call out to the FTP server log to pick up the IPs later. Can't get any easier than that.
who uses ICQ anymore though? or is this old school worming?
Doesn't Russia own ICQ and it was recommended not to use it (Without looking it up first) when we were "buddies" with the New Russian state
that was a great early messanger before weird shit started happening. no security in it what so ever. -
2022-10-25 at 4:48 PM UTC
Originally posted by slide22 who uses ICQ anymore though? or is this old school worming?
Doesn't Russia own ICQ and it was recommended not to use it (Without looking it up first)
that was a great early messanger before weird shit started happening. no security in it what so ever.
It makes a great pager. The executable is small and can be easily bound to a legit program without arousing any suspicion. -
2022-10-25 at 9:30 PM UTC
Originally posted by troon i'm pretty sure you misunderstood migh's "well shit", it didn't seem to be intended as you read it. but i do note how your interpretation of my words influences your thinking.
Without being able to read your body language or facial expression my interpretation of your words is the only thing to go off when you say some stuff. Therefore it is the only thing can use to construct a representation of you in my mind. It's one of those things people tend to do i think. Feel free to set the record straight or more crooked, by providing more words/thoughts/ideas, true or false. -
2022-10-25 at 9:31 PM UTC
Originally posted by ⠀⠀⠀⠀⠀⠀ The best way is take a old RAT that's detected and make it fully undetectable by changing just enough code to evade the strings in the viral definitions. You can use 10 or 15 of the best virus scanners out there to check your results after each code adjustment. Eventually, you get a really good RAT that's FUD. Then you bind it to some program and upload it everywhere and bind an ICQ notification to it to call out to the FTP server log to pick up the IPs later. Can't get any easier than that.
I'm more of a custom, or newfangled RAT person myself tbh.